Are we looking for USB storage media activity or all USB devices? Like, cameras 📸? Headphones 🎧? As for the timestamps, you’ll usually have first (setupapi log) and last connected. There are also OS specific timestamps, like first or last install, first connect since reboot etc. Windows USB artifacts, macOS. See Event Manager’s codes 20001 and 20002 for USB events for verification or if the registry was updated. Look at HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceClasses\ and HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\USB\<hardware id>\<instance id>\Device Parameters. More.
⚠️ On Windows, USB timestamps in registry will be updated when the registry itself gets update with a Windows update. Use Event Manager logs in these cases.
Look at HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\DeviceClasses\ and HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\USB\<hardware id>\<instance id>\Device Parameters.
Attached devices
Key 🔑: Software\Microsoft\Windows Portable Devices\Devices. For USB and other devices connected. The sub-key name contains the device’s serial number, name, disk ID (between {}), which is assigned by OS. This disk id can be used to track the device accross the system, for example, other registry values. But keep in mind, that not every USB device has a serial number. Dates and times - when the device was first inserted after the last reboot. FriendlyName - user-created name of the volume.
Key 🔑: Software\Microsoft\Windows NT\CurrentVersion\EMDMgmt. It was put as an extension of memory (aka ready boost). Checks to see if the USB device can be used to extend memory. Timestamps - when first inserted. Some entries are ending with some decimal number, this is a volume ID in decimal (convert to hex and get your GUID that can be used to correlated data with USBSTR in SYSTEM hive, see below). These should be converted to hex and used to trace the device accross the system.
Key 🔑: Software\Microsoft\Windows NT\CurrentVersion\Print\Printers for printers connected. This subkey may also contains some SIDs. I don’t quite understand yet, when this happens in general, but one case is when OneNote is used to share documets.
⚠️ Use information about USB devices from
SYSTEMhive to get more and validate this information.
USBs
Key 🔑: System\ControlSet001\Enum\USBSTOR or ControleSet001\Enum\USB (on my Win10 VM)
Key 🔑: System\MountedDevices - used to map devices to drive letters (not only USBs).
Contains ever connected USBs with their serial numbers (if they have these) and some additional information. 0064 - first installed, 0065 last installed, 0066 last arrival and 0067 last removal. The full path: Computer\HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Enum\USB\ROOT_HUB20\4&3af74d6&0\Properties\{83da6326-97a6-4088-9453-a1923f573b29}\. ⚠️ Note that ROOT_HUB20\4&3af74d6&0 is device specific, but {83da6326-97a6-4088-9453-a1923f573b29} is not.
⚠️ To view
Propertiessubkey admin 🧑💼 privileges are not enough for the live-registry. Install psexec and elevate to system by running the folling command from thepsexecfolder:.\PsExec.exe -i -s -d powershell.exe. In the PowerShell window that opens runregedit.
Device Parameters\PartMgr - gives a disk ID. PartitionTableCache may contains … surprise-surprise… a partition table! Wow… . For a GPT locate FF FF FF FF 00 00 00 00. 16 bytes right after that are for file system GUID. The next 16 bytes are unique volume GUID used to identify the volume accross systems as well as within one. It might be empty for a USB device. ContainerID - very important, can be used to filter event logs.
As for the MountedDevices… . If a device doesn’t have a serial number, it’ll be assigned a machine assigned number aka unique instance ID (not consistent accross multiple systems). If the second character is & - not a a serial number.
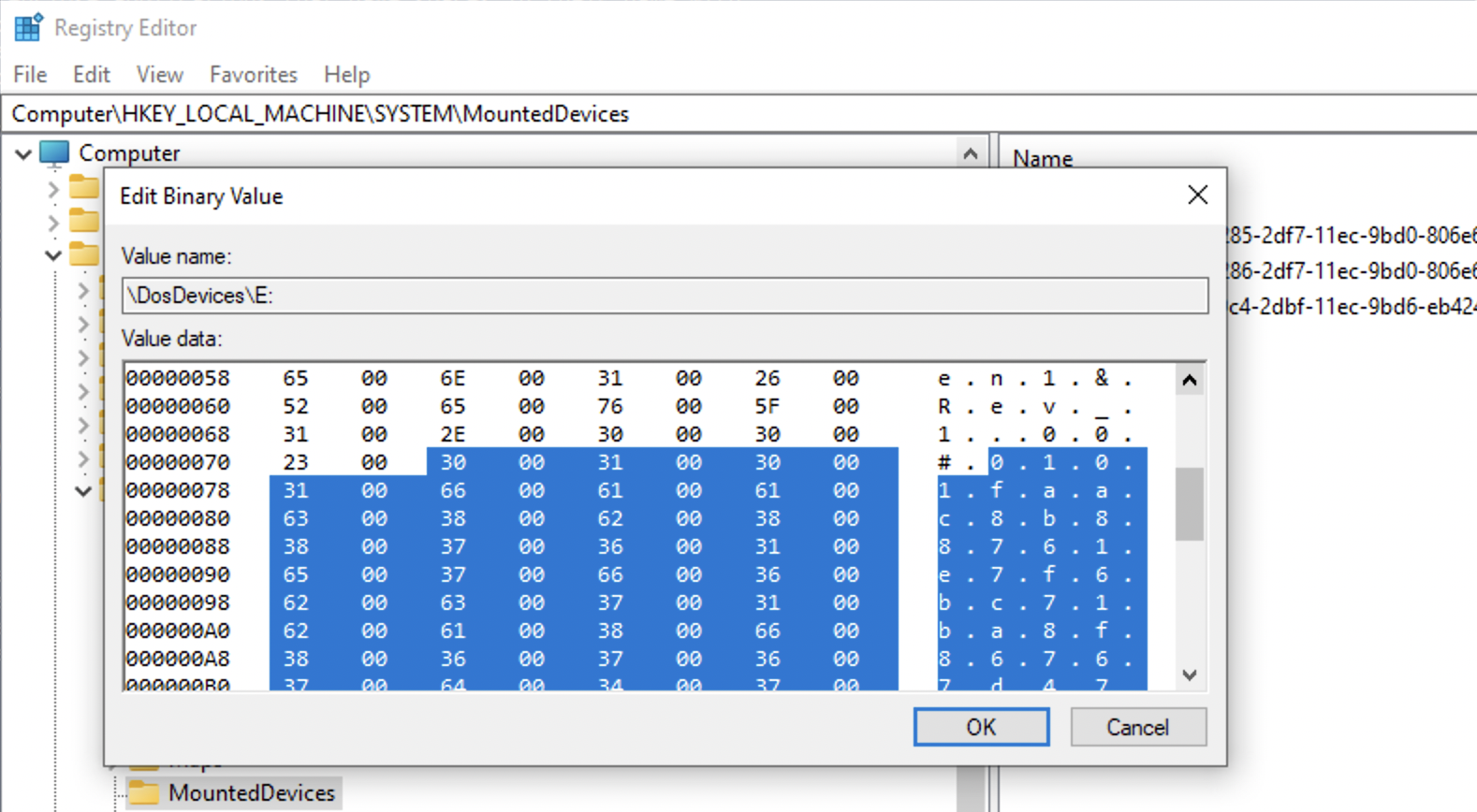
❓ How do I find it? Lot’s of gibberish is all I see…
✍️ Just find the device name, search for the
#sign, check after it and up until the next#right before a GUID contained withing{}.
This is an example of a USB device with a serial number that will be reletively unique (not all vendors borther giving each USB drive a separate serial number).
And here is an example of a machine assigned id. Note, that the second symbols is &.
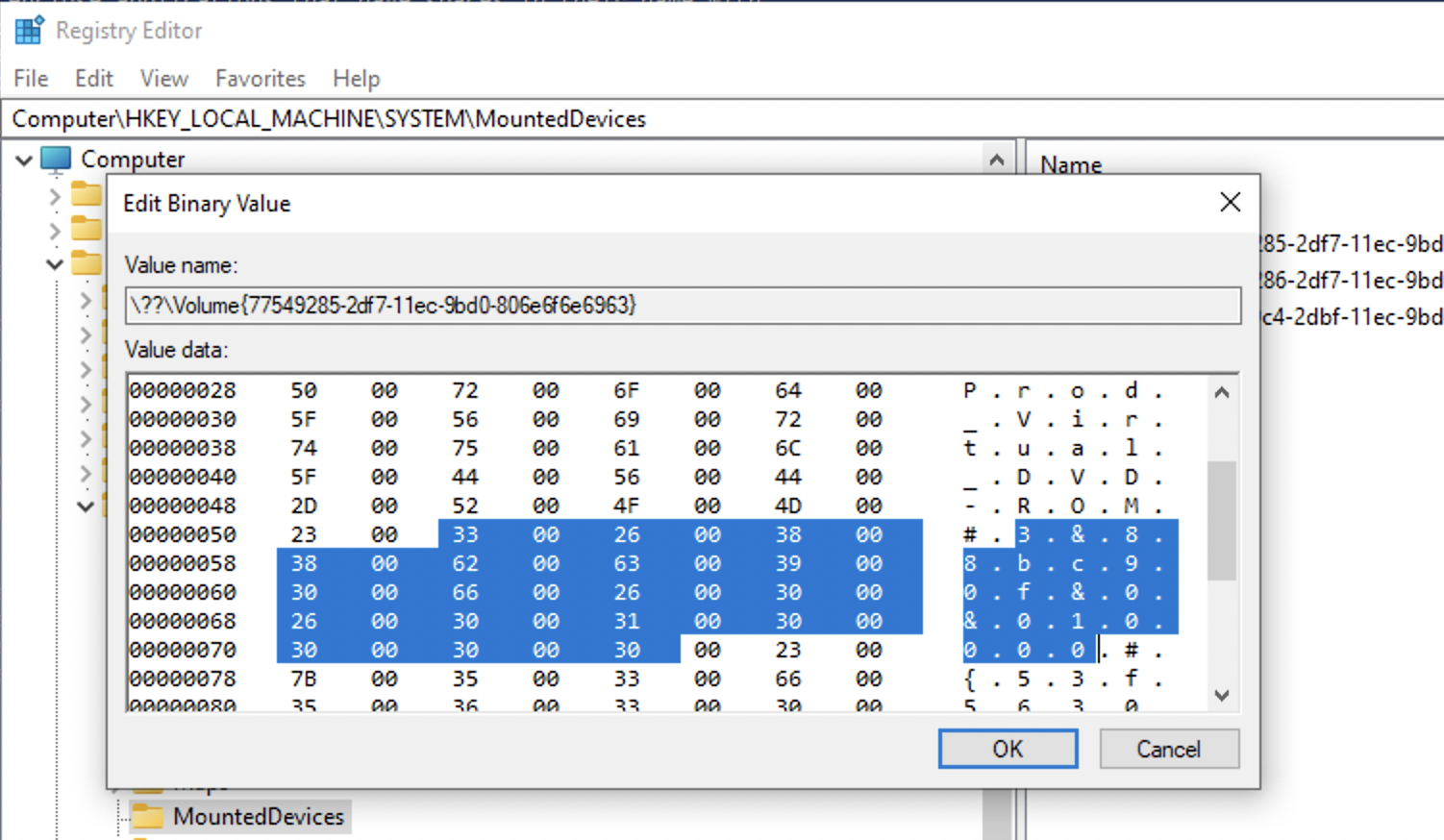
The value that follows the serial number/uniqueid right after the second # and encolsed between {} is the disk id.
Logs
USBDevicesLogs: Path: C: \Windows\setupapi.log
USBDevicesLogs: Path: C: \Windows\inf\setupapi.dev. log
Mounted Devices
Key 🔑: NTUSER\MountPoints2.
If you link volumes from system-wide 🔑 MountPoints and 🔑 USBSTR, we can link a device to a specific user. This 🔑 also shows all systems connected by the current user (useful for RDP investigations).
🗒️ TODO: How to link, screenshots.
ManagedByApp
Key 🔑: Software\Microsoft\Windows\CurrentVersion\AppModel\SystemAppData\Microsoft.Windows.Photos_8wekyb3d8bbwe\PersistedStorageItemTable\ManagedByApp.
Tracks images opened with Microsoft application. Shows volume GUID (use other USB-related registry to assemble the picture), file path, data and time ⏰. LastUpdateTime shows when the files was … . This date and time is very close LastInteracted from ShellBags. Go to MountedDevices in SOFTWARE hive to find the device by the volume GUID and the to SYSTEM’s USBSTR -> PartitionTableCache.
This information is very useful for child abuse cases.
ShellBags
Key 🔑 : Local Settings\Software\Microsoft\Windows\Shell\BagMRU . Values: MRUListEx, NodeSlot, Subkeys.
Key 🔑 : Local Settings\Software\Microsoft\Windows\Shell\Bags. Values: Shell, will have folder’s GUID.
For more info refer to the Shellbags article.
Event Logs
Security 6416: A new external device was recognized by the system
Event ID 219 is logged when a device is plugged into a Windows-based system
Plug’n’Play
By default, the SetupAPI text logs are located in the %SystemRoot%\Inf directory.
To enable event categories for the SetupAPI logs, create (or modify) the following REG_DWORD registry value:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Setup\LogMask. More here.


