This article explains how SSL and its successsor work.
Intro
SSL makes use of assymmetric encryption for verification and symmetric encryption for data exchanging. Common ports: 443, sometimes 5443. TLS is an improvement. SSL is not being used too much since it’s not very secure (exploiting it requires a lot of knowledge and effort though), however, the protocol scheme is still called SSL/TLS.
Preamble
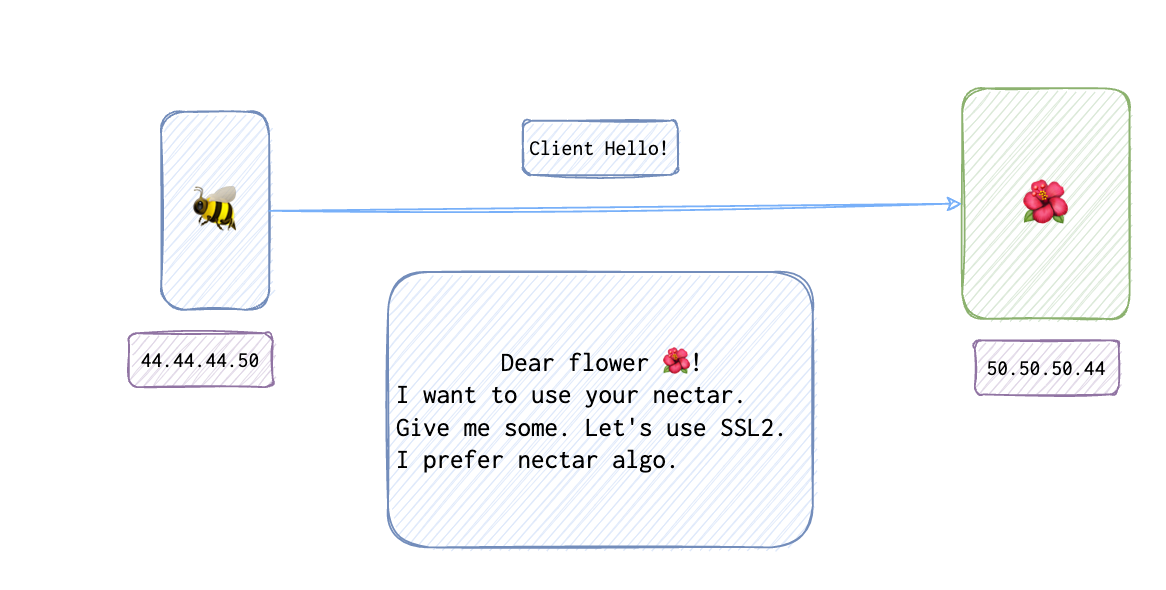
Bob 🐝 salutes the 🌺 server . This message is called Client Hello. It contains the following things:
- SSL version that the client supports
- random data
- encryption algorithm
- session ID (*optional)
- key exchange algorithm
- compression algorithm
- MAC
The 🌺 server replies with … surprise-surprise Server Hello. It contains the following things:
- SSL version
- Session ID:
12345 - server’s certificate
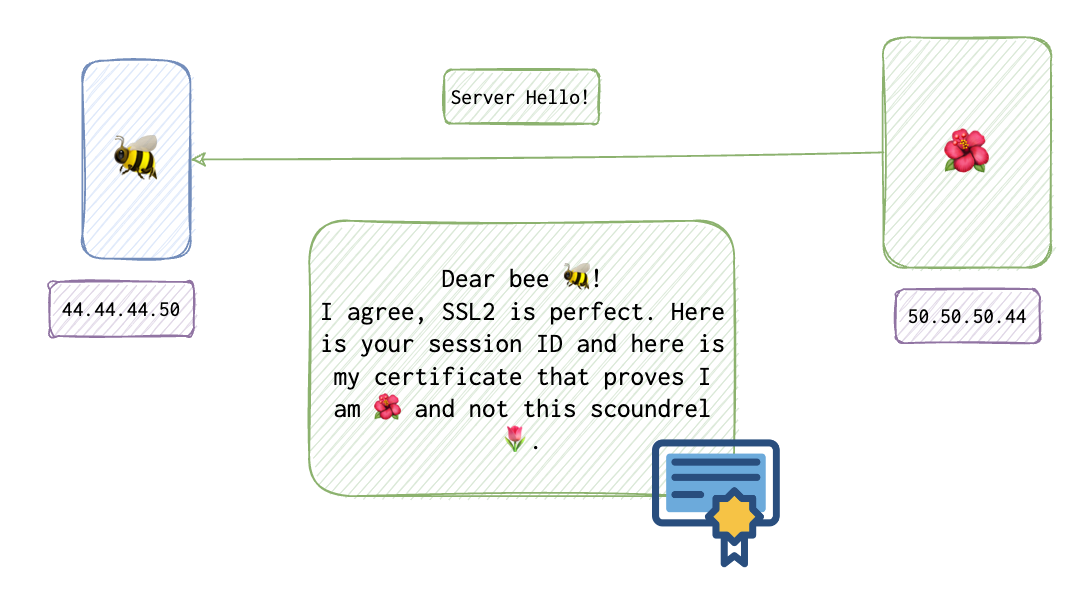
The 🌺 server stops the babbling with Hello done message.

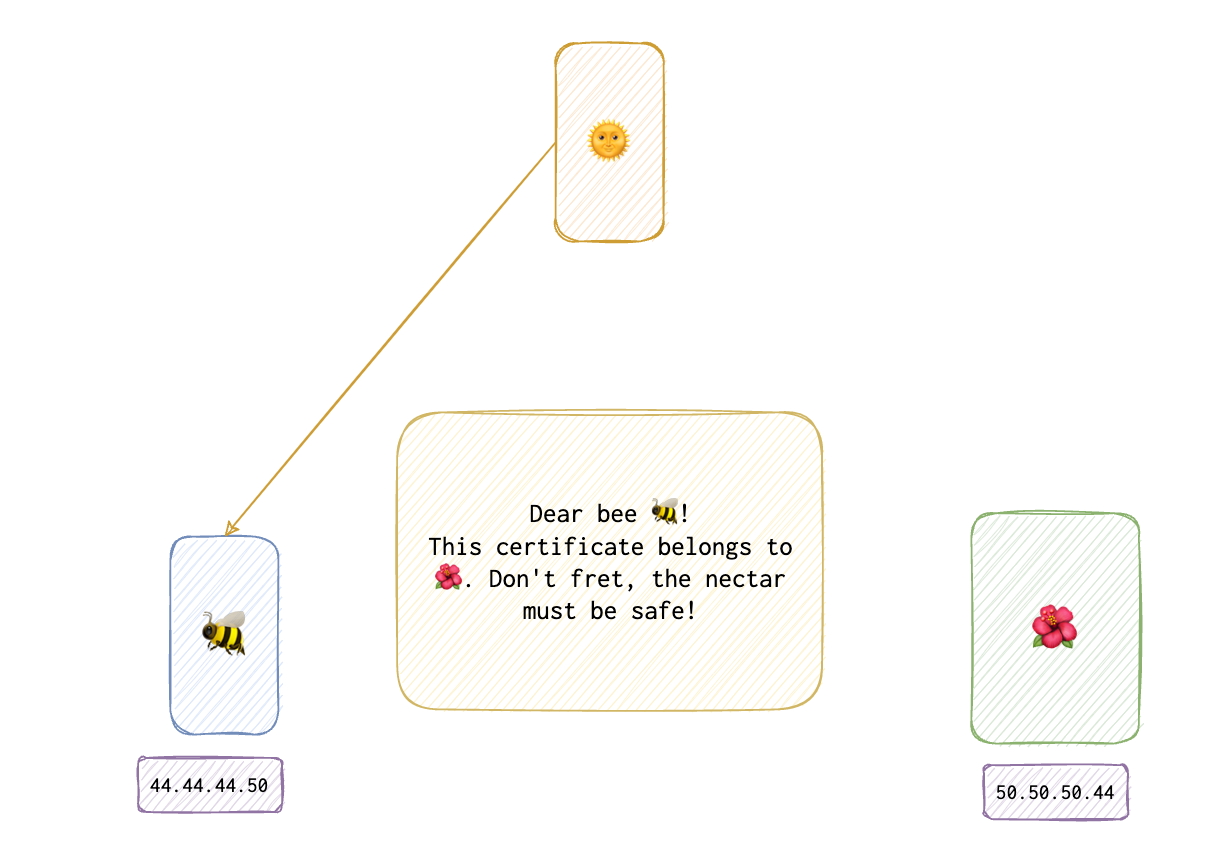
Bob 🐝 checks the certificate at the certificate authority.
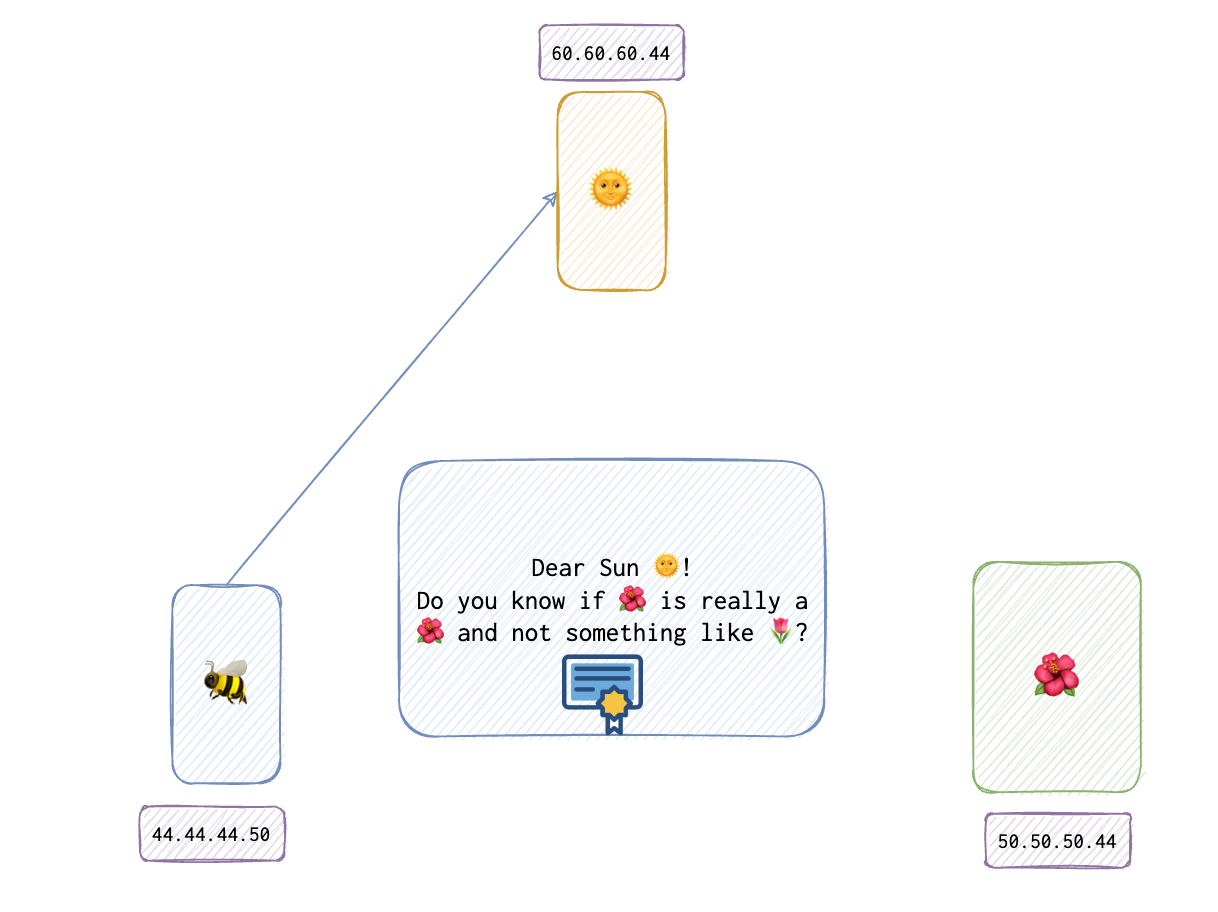
Let’s assume that the certificate is ok.
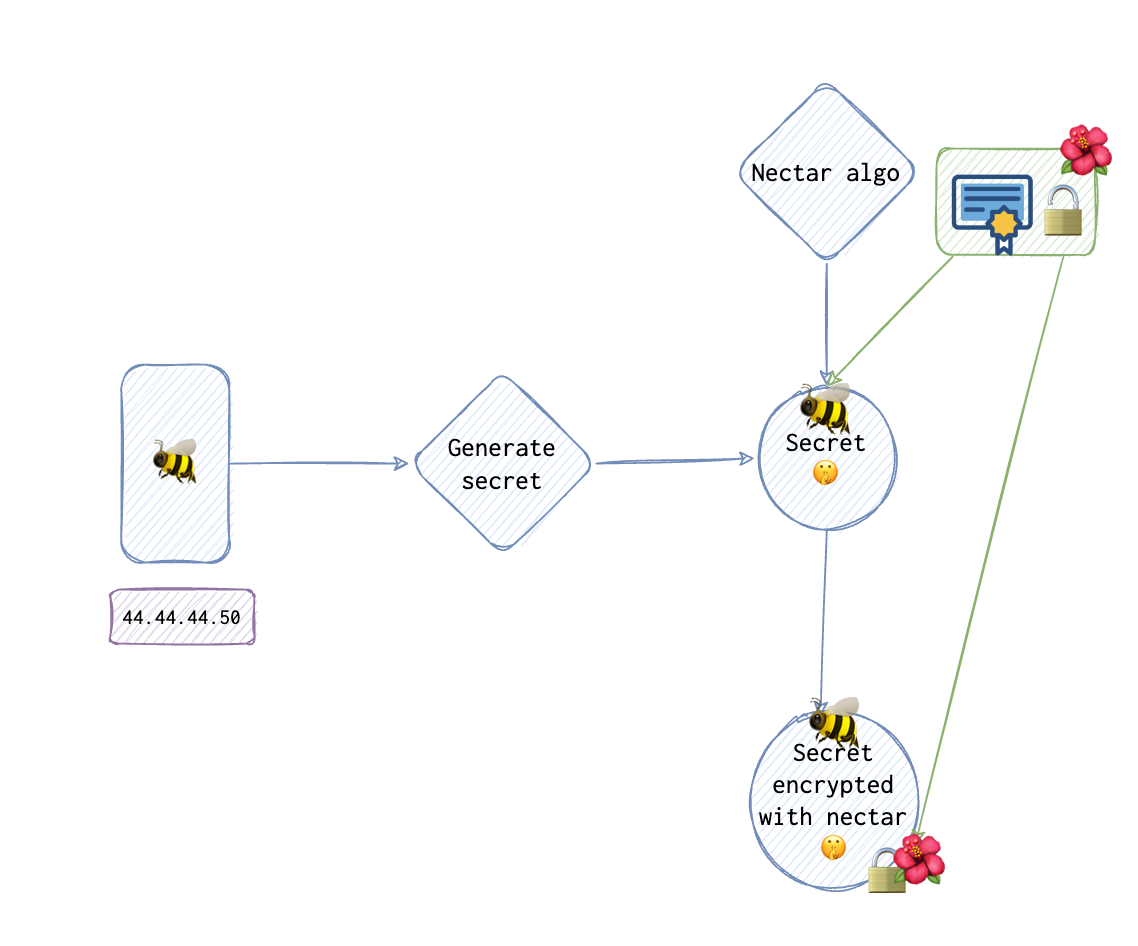
If the certificate is valid, Bob 🐝 generates a secret using an algoruthm G() and random data r as input to get a secret. This secret is then encrypted with some function that both Bob 🐝 and the 🌺 server have agreed on: Enc(secret). Then Bob 🐝 sends Client Key Exchange message. This message is encrypted using nectar (or any other asymmetric algo like RSA) with the server’s 🌺 public key 🔓.
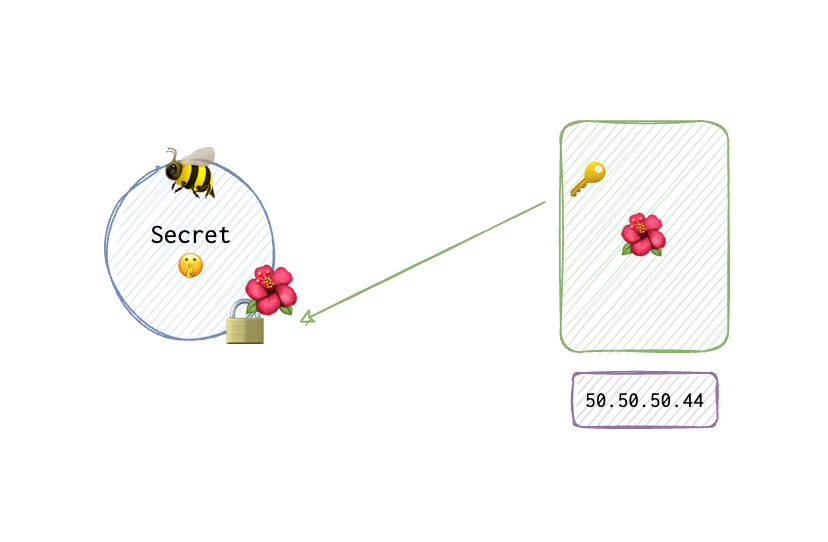
Upon receiving this message, the 🌺 server decrypts the secret 🤫.
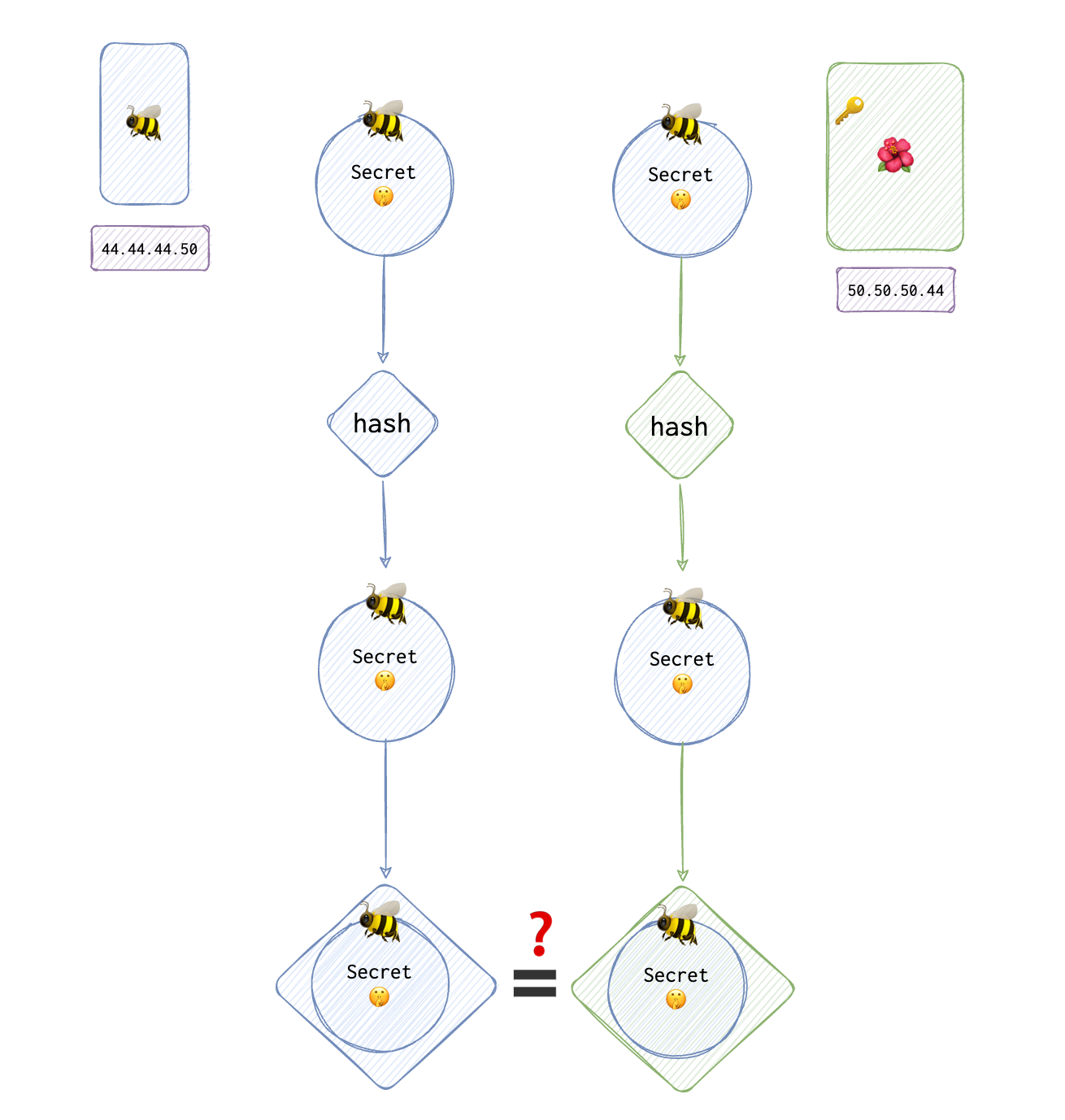
It then computes the hash for it 🤫. Bob 🐝 does the same and sends this hash to the 🌺 server in the Change Cipher Spec Finished hash message.
If the hashes match, the 🌺 server sends Finished message.
That’s how the connection is established. One more thing to note, if the session is not expired, then Bob 🐝 sends his session ID in the first, Client Hello message. If it exists, they resume from the step when Bob sends a Finished message.
TLS improvements
TLS is basically the same, but some algorithms were deprecated. Besides, TLS supports client authentication as well (the additional steps are below). Uses DES/RSA + keyed MAC.
After Server hello, the 🌺 server sends a Server hello done.
Bob 🐝 creates a master secret +SID. Now Bob 🐝 has to send his certificate Enc(Premaster secret) encrypted with the 🌺 server server’s 🌺 public key 🔒. The rest is the same.
Record protocol
- Fragment and reassemble data
- optional comression and decompression
- Apply MAC
- encryption
How SSL certificates are verified?
References
https://sectigostore.com/blog/ssl-vs-tls-decoding-the-difference-between-ssl-and-tls/
🗒️ https://stackoverflow.com/questions/188266/how-are-ssl-certificates-verified


