Case Overview
The Target Corporation is an American retailing company, founded in 1902 and headquartered in Minneapolis, Minnesota. It’s the second largest discount retailer in the United States. Target operates 1,916 stores in the United States, and also began operations in Canada in March of 2013. In December 2013, a data breach of Target’s systems effected up to 110 million customers. The attackers stole around 110 million customers’ PII. They had all the IDS/IPS and stuff and were PCI-DSS compliant.
Attack layout
Stage 1. Recon
The target had some internet portal for vendors that revealed their technologies. The attacker managed to get one of the vendors Fazio. Recon stage against Fazio now.
Stage 2. Weaponisation
The attacker created e-mails with a malware as an attachment (doc or pdf).
Stage 3. Delivery
Sent the emails to the vendor (phishing attack). Recorded passwords with this malware which was the key to the Target’s external billing system. The attcker used this service to make his way through the Target’s perimeter.
Stage 4. Exploitation
RAM scrappy malware and exfiltration malware recorded the data and sent it to the attacker. Probably due to default creds and exploting the Target’s IT management.
Stage 5. Installation
Why that was successful? May be the network security was weak. Uploaded their RAM scarpping malware to the POS terminals.
Stage 6. C&C
The data was sent to different server, one of them was in Russia, plaint text, FTP. They’ve been inside for about a month.
Stage 7. Action
December 12, 2013, the Target is notified by US Department of justice that their stolen credit card creds have been identified on a Russian dark net site. Three days lateer most of the malware was removed.
Post-Incident Activity
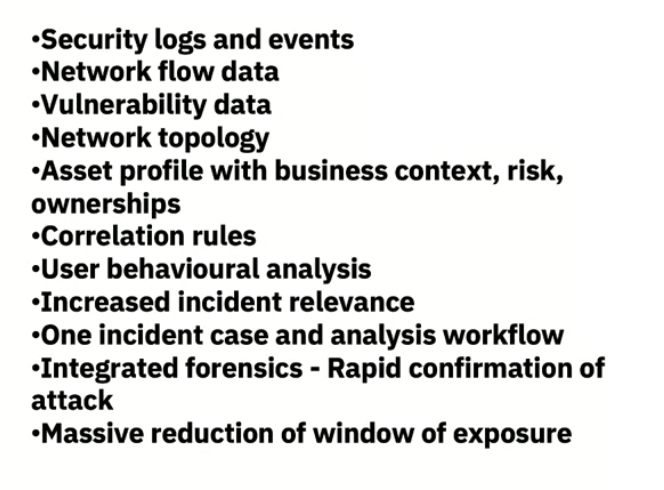
The first alerts were recorded on 30th of November, but were disregarded. Probably due to the fact the the endpoint solutions do not communicate with one another. It’s hard sometimes to tell that the incident took place by just looking at a single event.
The Target has to pay $18,5 million for this breach.